Image Steganography Project [Data hiding]
Image steganography is a type of information security method that involves concealing hidden messages in ordinary digital photographs to communicate secretly. In other words, image steganography project is the practice of concealing sensitive information within an image or video file. A basic example of concealing a text message within an image is provided.
Summary of Image Steganography
Image steganography is the practice of concealing data, such as text, pictures, or audio files, within another image or video file. The current research seeks to utilize spatial domain steganography for one picture with another image. Only with suitable decoding techniques can this concealed information be recovered.

- Spatial domain – Payload
- Transform domain- Undetectability
Image Coded Format based Steganography
- Encrypted (AES based image)
- Compressed (JPEG 2000)
- RAW (uncompressed) ( BMP, PNG)
Secret data format based steganography
- Plain / Raw
- Compressed
- Encrypted
- Compressed- Encrypted
These are the primary mechanisms, terms, and techniques that can be used for image steganography. For the type of images, these steganography techniques can be useful. In the following, let’s understand how this security technology works is given.
“This article provokes you more innovative research ideas and information about the Image Steganography project!!!”
How does Image steganography Work?
In image steganography, a message is hidden in plain text by changing the values of a few pixels chosen using an encryption algorithm. The image’s recipient must be aware of the same technique to determine which pixels to choose to extract the message. The two key steps are as follows:
- Encryption: Storing the text within an image i.e. called embedding
- Decryption: Extracting the text that is hidden within the image i.e. called extraction
Here we have two kinds of steps for Image Steganography which are also has more important in this part. For your easy purpose, we have selected a small classification. We are here to help you for developing a project. You can contact us all the time. In this institute, our research scholars are well-known in all kinds of subjects.
What are the tasks in Image Steganography?
- Hide Sender
- Hide Receiver
- Hide Secret Data
When compared to stego-analysis, the field of steganography has progressed more (tools or techniques). Furthermore, there is no universal and efficient detection hiding strategy or tool because of the large number of steganography approaches available with various concealing locations and media. Similarly, several challenges must be overcome in the identification of concealed data.
Research Challenges of Image Steganography Project
This section looks at the main difficulties and obstacles that data-concealing researchers and cyber or forensic examiners have while building a steganalysis approach, tool, or search engine.
- Require accurate methodology
There are no adequate standards offered for investigators that will allow forensic and cyber specialists to hunt for concealed material methodically. It is difficult for forensic specialists to pursue the procedure of steganalysis for the identification and extraction of hidden data without any guidelines.
- Performance tradeoff
The first and most challenging task for a good steganography approach is to find an appropriate trade-off between the essential criteria of steganography, such as imperceptibility, capacity, resilience, and security.
- Higher time consumption
Another difficulty for forensic examiners is the interminable time necessary to check the suspect’s network traffic or system due to the large storage capacity of the hard disc, which takes hours to find.
- Hard Stego Extraction
Typically, forensic or cyber specialists focus on determining whether any known data concealing technique or application has been installed and utilized rather than extracting concealed data. Forensic and cyber specialists still have a difficult challenge in extracting concealed data.
- Complex recover the hidden data
From a cyber and forensic standpoint, it is still one of the most difficult problems to solve.
- Tough to recover the uninstalled program
There is a plethora of steganography software and tools available, many of which are simple to set up and use. The work of detection for forensic examiners is growing more difficult by the day since tools can be erased or transferred to removable devices such as pen drives, hard discs, and other storage devices, from which they can be accessed directly.
- Systematic Assessment
Another problem for cyber and forensic investigators is that many of them fail to check a defendant’s system for data concealing tools or software frequently. In comparison to data concealing tools, there are few tools available for forensic investigators that are intended specifically for a certain sort of steganography approach.
In general, the stego picture has a greater PSNR value based on the PSNR value of each image. As a result, this new steganography method is highly effective at hiding data within pictures. SIS can be used by a variety of users who want to keep the data inside a picture hidden from prying eyes.
Which Algorithm is used in Image Steganography?
The technique of steganography has five parts which are as follows,
- Statistical
- Vector Embedding
- Distortion, Masking and Filtering
- A Spatial Domain
- Transform Domain
- Spread Spectrum
Further, the spatial domain has three classes of techniques such as LSB, PVD, and BPC. And transform domain has three classes of techniques that are DFT, DWT, and DCT.
For any type of steganography application, these techniques can be very useful. We are giving the best guidelines when using any techniques and technologies. It should be more creative and handpicked points. You can get any research help, image steganography project paper writing, conference paper writing, paper publications, and thesis writing support you can communicate with us.
How to implement image steganography using Python?
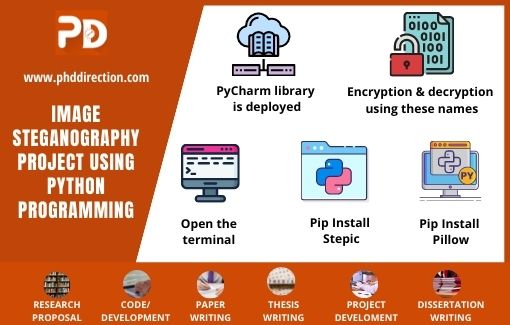
- Initially, Python IDLE is opened and PyCharm library is deployed for image-based steganography.
- Then create the program files for encryption and decryption using these names.
- Open the terminal and type the below-listed commands to install the respective libraries.
- Pip Install Stepic
- Pip Install Pillow
Stepic
A Python package for concealing data within an image by changing the picture’s colors gradually. These changes are typically undetectable to the naked eye, but they are detectable by machines.
Pillow
Image processing features such as reading, editing, and storing images of various formats are supported by this Python Imaging Library (PIL).
Type the Python code listed below into the encryption.py file. After that, execute the code to get the results shown below. For students’ benefit, we are creating the easiest method. They can easily adapt the concept and throw the concept you will get a good future. We are here to make your comfortable elements. Next, we can see the important features here. This idea from our team members. That idea should be more innovative.
Process of Encryption
Type the Python code described below into the encryption.py file. Then execute the code to get the results shown below.
- Firstly, import Python libraries which are necessary
- Using PIL, image is imported
- Use Stepic library
- Store the secret message and open it
- Mention the secret message in the image
- Implement Conversion_Operation for the image into UTF-8 format
- Use the Encode () operation using message passing
- With the use of Encode () operation, hide the input image
- Mention the name and new stego image is generated
Decryption Process
Type the code provided below into the decryption.py file. Then, as demonstrated below, run the code to receive the hidden secret message.
- To decrypt the message, firstly add important libraries
- Use of PIL to add the images
- Add steps
- Use the image that is hidden for text extraction
- Image is forwarded for the Decode function
- Produce the output as the secret message [look in the STRINGS]
- Return the final message as an output
There is a wide range of datasets are available for processing steganography. Among the huge list of datasets, we are specified here very few for your reference. Without datasets, we can test or perform experiments for any idea in image steganography project. Hence, looking into these datasets can be useful for you to understand them.
Datasets Available for Image Steganography Project
- NRCS
- RSP Database
- Labelled Faces in the Wild
- Columbia University Image Library
- USI-SIPI
- INRIA Holidays
- Stanford Dogs Dataset
- Washington Image Database
- Kodak Image Database
- Visual Geometry Group
- Boss base
- CBIR
- YFCC100M
- UCID
- CIFAR-10
- LabeIMe
- ImageNet
- MS-COCO
- PASCAL VOC
- BOWS2
Generally, our team is sought by researchers around the world as we ensure to provide you with complete work privacy, massive research resources that are taken from benchmark references and confidential research guidance online. Our technical experts keep themselves updated to help you out in all the latest and emerging technologies. We will now have a look into the important recent steganography projects.
Future Research Directions in Image Steganography
New standards
H.265/HEVC is the most recent compression standard, which is still relatively new to academics, but it will soon replace the others because of its numerous sophisticated capabilities. As a result, from the standpoint of steganography, it appears that there is a lot of room to investigate this field to build a steganography approach. Furthermore, because H.265/ HEVC is the new standard for steganography, it is likely to be used by criminals and terrorists; hence, algorithms and techniques to detect the presence of concealed data will be required.
Neural network models can also be utilized to improve the steganography technique’s detection accuracy. It could be useful in identifying steganography in videos, which are notoriously tough to study and detect.
New Steganalysis tools
The identification and extraction of concealed data are outweighed by tools and strategies for embedding. Thousands of steganography tools are accessible for no cost or for free; however, the same cannot be said for steganalysis, which necessitates more work and a thorough grasp of the steganography tools and methodologies. As a result, cyber- and forensic specialists must create more effective steganalysis techniques.
To summarize, we are giving genuine and the most trusted writing projects and assignments projects with the help of our students. If you need any kind of project help or a reference you should directly contact our research institute. We will make the best image steganography project for you.
Why Work With Us ?
Member Book
Publisher Research Ethics Business Ethics Valid
References Explanations Paper Publication
9 Big Reasons to Select Us
Senior Research Member
Our Editor-in-Chief has Website Ownership who control and deliver all aspects of PhD Direction to scholars and students and also keep the look to fully manage all our clients.
Research Experience
Our world-class certified experts have 18+years of experience in Research & Development programs (Industrial Research) who absolutely immersed as many scholars as possible in developing strong PhD research projects.
Journal Member
We associated with 200+reputed SCI and SCOPUS indexed journals (SJR ranking) for getting research work to be published in standard journals (Your first-choice journal).
Book Publisher
PhDdirection.com is world’s largest book publishing platform that predominantly work subject-wise categories for scholars/students to assist their books writing and takes out into the University Library.
Research Ethics
Our researchers provide required research ethics such as Confidentiality & Privacy, Novelty (valuable research), Plagiarism-Free, and Timely Delivery. Our customers have freedom to examine their current specific research activities.
Business Ethics
Our organization take into consideration of customer satisfaction, online, offline support and professional works deliver since these are the actual inspiring business factors.
Valid References
Solid works delivering by young qualified global research team. "References" is the key to evaluating works easier because we carefully assess scholars findings.
Explanations
Detailed Videos, Readme files, Screenshots are provided for all research projects. We provide Teamviewer support and other online channels for project explanation.
Paper Publication
Worthy journal publication is our main thing like IEEE, ACM, Springer, IET, Elsevier, etc. We substantially reduces scholars burden in publication side. We carry scholars from initial submission to final acceptance.